
Thousands of phones and routers swept into proxy service, unbeknownst to users
getty images
Crooks are working overtime to anonymize their illegal online activities by using the devices of thousands of users, two unrelated reports published Tuesday reveal.
The first report from security firm Lumen Labs says that approximately 40,000 home and office routers have been implicated in a criminal enterprise that anonymizes illegal Internet activities, with 1,000 new devices being added every day. The malware responsible is a variant of TheMoon, a malicious code family dating back to at least 2014. In its early days, TheMoon almost exclusively infected Linksys E1000 series routers. Over the years it evolved to target Asus WRT, Vivotek Network Cameras, and several D-Link models.
In the years since its introduction, TheMoon's self-propagating behavior and increasing ability to compromise a broad base of architectures enabled a growth curve that attracted attention in security circles. Recently, the visibility of the Internet of Things botnet decreased, leading many to assume it was inactive. Surprising researchers at Lumen's Black Lotus Lab, TheMoon added 6,000 ASUS routers to its ranks during a 72-hour period earlier this month, a sign that the botnet is as strong as it's ever been.
Even more surprising than the discovery of over 40,000 infected small office and home office routers located in 88 countries is the revelation that TheMoon is enrolling most of the infected devices into faceless, anonymous illegal activities that are being sold on online crime forums. It is a service. The proxy service gained widespread attention last year after this profile by KrebsOnSecurity.
“This global network of compromised SOHO routers gives actors the ability to bypass some standard network-based detection tools – particularly those based on geolocation, autonomous systems-based blocking, or TOR blocking,” Black Lotus researchers wrote on Tuesday. Focused.” He added that “80 percent of faceless bots are based in the United States, meaning accounts and organizations within the US are the primary targets. “We suspect that the majority of criminal activity is likely password spraying and/or data exfiltration, particularly towards the financial sector.”
The researchers further said that more traditional methods of anonymizing illegal online behavior have fallen out of favor with some criminals. For example, VPNs may log user activity despite some service providers' claims to the contrary. Researchers say the possibility of the Tor anonymity browser being tampered with may also have scared off some users.
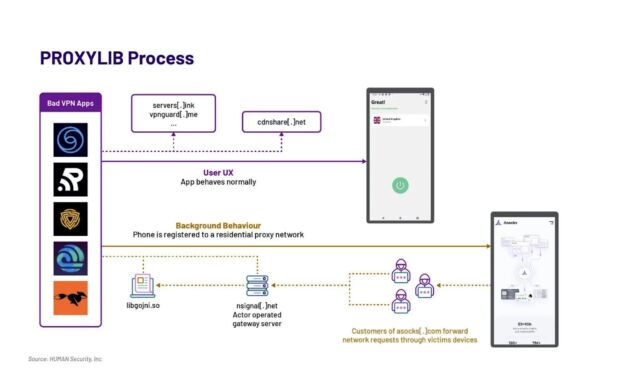
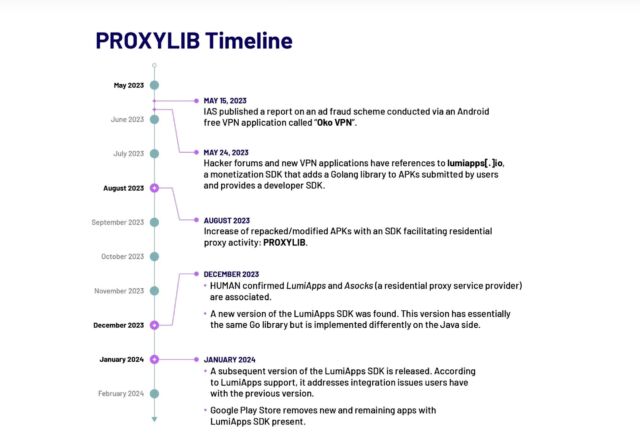
The second post comes from Satori Intelligence, the research arm of security firm HUMAN. It discovered 28 apps available in Google Play that enrolled their devices into a residential proxy network of 190,000 nodes to unknowingly allow users to anonymize and obfuscate others' Internet traffic.
human being
ProxyLib, the name Satori gave the network, has its roots in Oko VPN, an app that was removed from Play last year after revelations that it was using infected devices for ad fraud. The 28 apps Satori discovered all copied Oko VPN code, which made them nodes in residential proxy service Assoc.
human being
The researchers identified a second generation of ProxyLib apps developed through Lumiapps(.)io, a software developer kit that deploys exactly the same functionality and uses the same server infrastructure as Oko VPN. The LumiApps SDK allows developers to integrate their custom code into the library to automate standard processes. This allows developers to do this without creating a user account or recompiling the code. Instead they can upload their custom code and then download a new version.

human being
“Satori has observed individuals in the wild using the LumiApps toolkit,” the researchers wrote. “Most of the applications we identified between May and October 2023 appear to be modified versions of known legitimate applications, which further indicates that users do not need access to the source code of applications to modify them using LumiApps . These apps are largely named 'mods' or denoted as patched versions and shared outside the Google Play Store.
Researchers don't know whether the 190,000 nodes containing Asock at its peak were composed exclusively of infected Android devices or whether they included other types of devices compromised by other means. Either way, the numbers indicate the popularity of anonymous proxies.
People who want to prevent their devices from being drafted into such networks should take some precautions. The first is to resist the temptation to continue using equipment if it is not supported by the manufacturer. For example, most of the devices featured in TheMoon have reached end-of-life status, meaning they no longer receive security updates. It is also important to install security updates in a timely manner and disable UPnP unless there is a good reason for it to be on and then allow it only for essential ports. Users of Android devices should install apps sparingly and only after researching the reputation of both the app and the app manufacturer.



